
Why are top university websites serving porn? It comes down to shoddy housekeeping.
Hundreds of subdomains from dozens of universities have been hijacked by scammers.

Hundreds of subdomains from dozens of universities have been hijacked by scammers.

Technically speaking, there's no practical benefit to use PQC. So why is it being used?

Anthropic's tightly controlled rollout of Claude Mythos has taken an awkward turn. After spending weeks insisting the AI model is so capable at cybersecurity that it is too dangerous to…

When authentication fails, things can go very, very wrong.

A stubborn misconception is hampering the already hard work of quantum readiness.
Grinex says needed hacking resources "available exclusively to... unfriendly states."

Here's which players are winning the race to transition to post-quantum crypto.
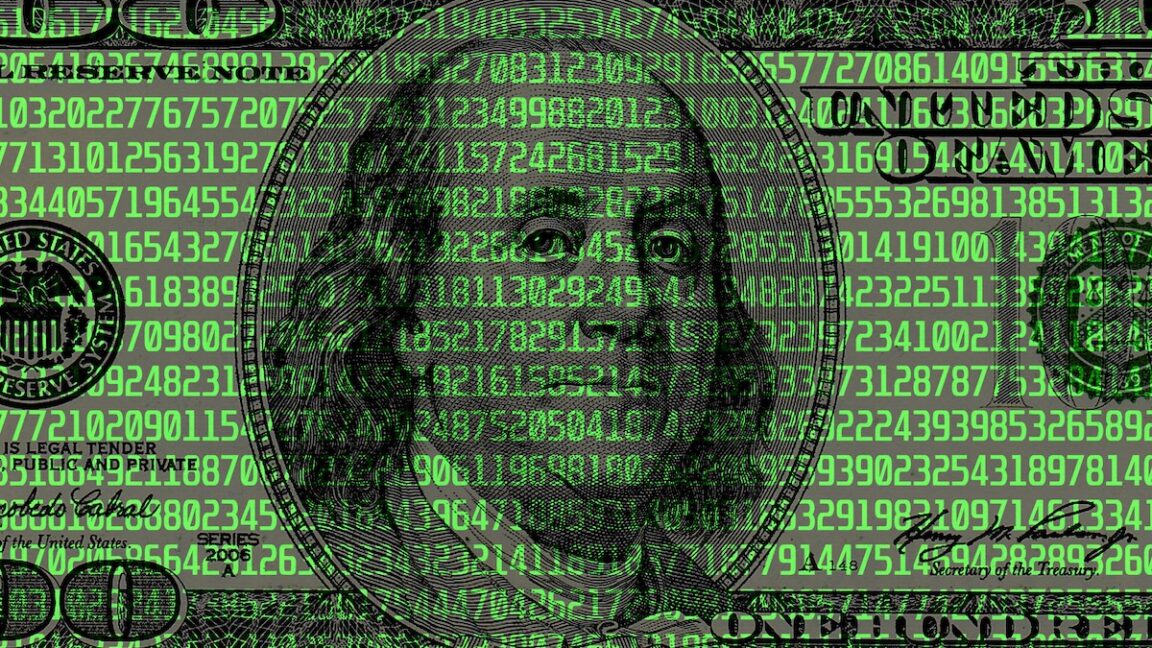
Leading security firms and enterprises join OpenAI’s Trusted Access for Cyber, using GPT-5.4-Cyber and $10M in API grants to strengthen global cyber defense.
OpenAI expands its Trusted Access for Cyber program, introducing GPT-5.4-Cyber to vetted defenders and strengthening safeguards as AI cybersecurity capabilities advance.
OpenAI responds to the Axios supply chain attack by rotating macOS code signing certificates, updating apps, and confirming no user data was compromised.

As the US and Israel's war has ramped up, so too have hacks on US industrial sites.
End-of-life routers in homes and small offices hacked in 120 countries.

The viral AI agentic tool let attackers silently gain admin unauthenticated access.

GDDRHammer, GeForge and GPUBreach hammer GPU memory in ways that hijack the CPU.

No, the sky isn't falling, but Q Day is coming, and it won't be as expensive as thought.

Company warns entire industry to move off RSA and EC more quickly.
Development houses: It's time to check your networks for infections.
Admins: Sorry to say, but it's likely a rotate-your-secrets kind of weekend.

Internet-exposed devices that give BIOS-level access? What could possibly go wrong?
Unicode that's invisible to the human eye was largely abandoned—until attackers took notice.

Company says it doesn't know how long it will take to restore its Microsoft environment.